Why ITAD Is More Complex Than You Think
Why ITAD Is More Complex Than You Think
Key Takeaways
- ITAD is not a disposal event. It is a lifecycle process with roots at the point of acquisition.
- A compliant ITAD program rests on four pillars: data security, regulatory compliance, value recovery, and environmental responsibility.
- Enterprises operating across multiple countries face materially different ITAD requirements, particularly following the Basel Convention amendments that took effect in January 2025.
- Data liability does not end when a device powers down. Risk persists through every stage of disposition until certified destruction is confirmed.
- How assets are acquired -- owned versus leased -- shapes how complex and costly ITAD will be at end of life.
- Documented chain of custody and certified data destruction are non-negotiable, regardless of company size or industry.
Table of Contents
Author: Simon Harrsen, EVP North America, CHG-MERIDIAN
Published: May 1, 2026

What Is IT Asset Disposition?
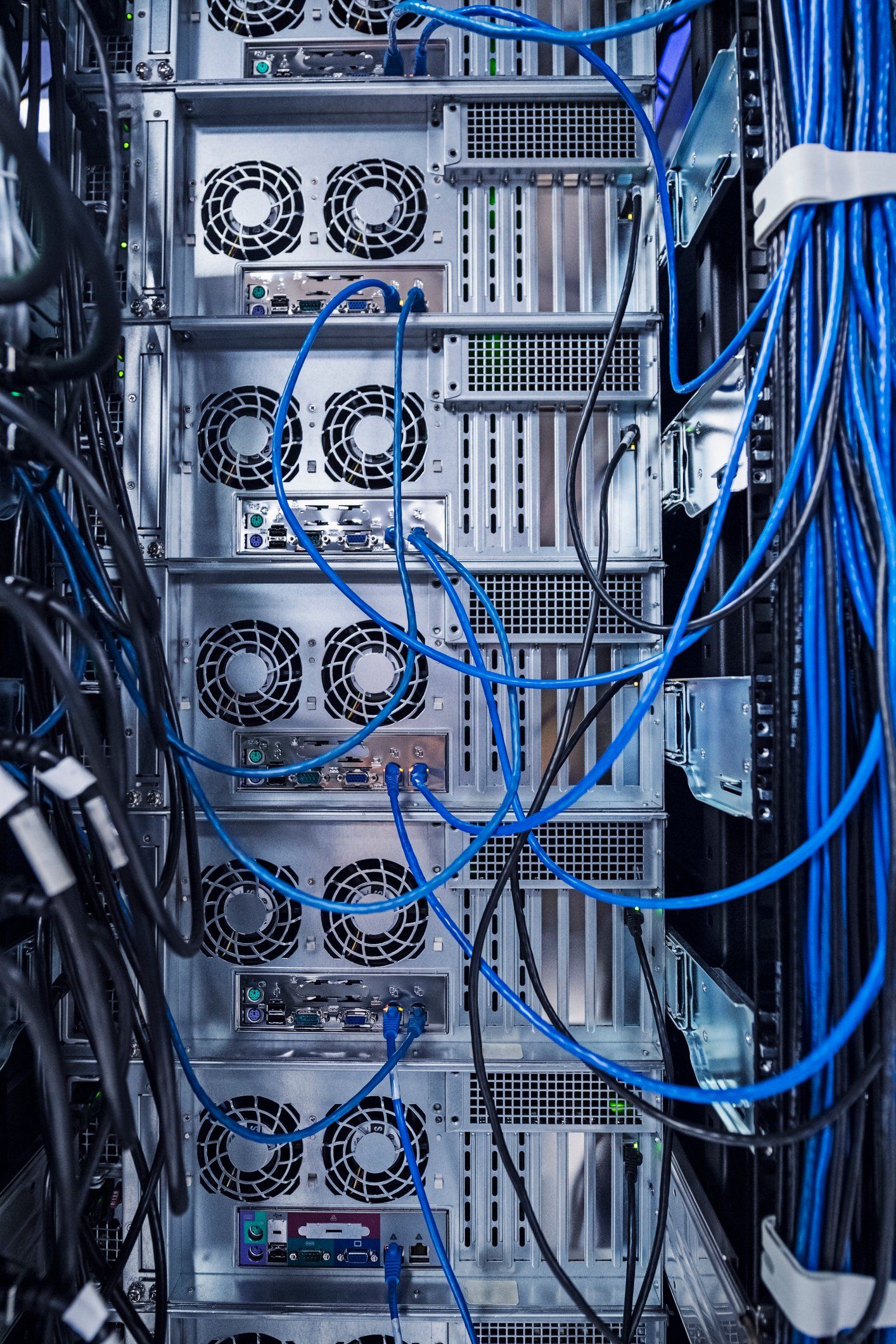
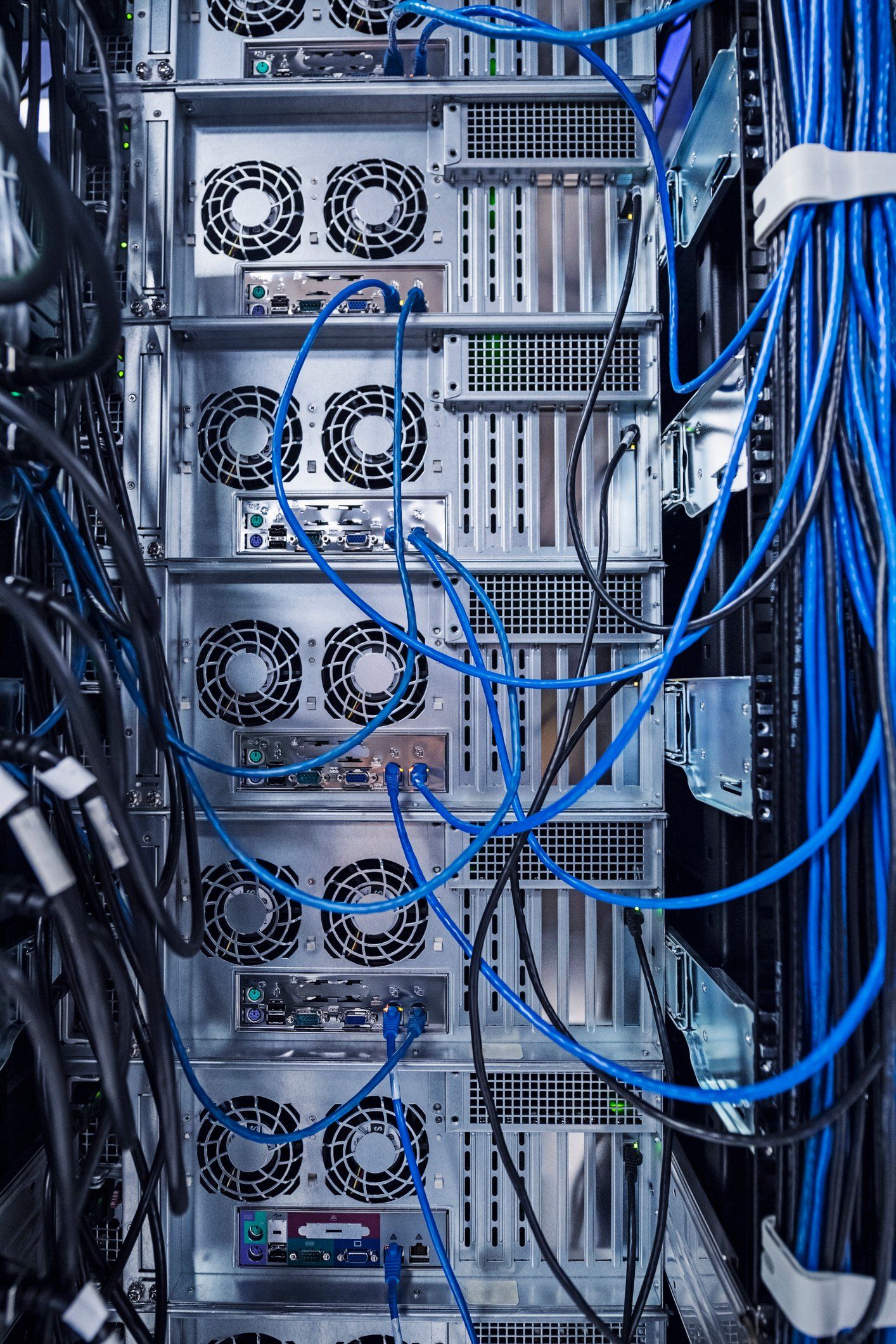
IT asset disposition, commonly called ITAD, is the structured, documented process of retiring end-of-life technology hardware in a way that protects data, satisfies regulatory obligations, recovers residual value where possible, and minimizes environmental impact. It applies to the full range of enterprise hardware: servers, desktop workstations, laptops, mobile devices, network switches, storage arrays, backup tapes, and any device that stores, processes, or transmits data.
ITAD is not recycling. Recycling is one possible outcome within an ITAD process. The distinction matters because the two are not interchangeable from a compliance or liability standpoint. A recycler processes materials. An ITAD program manages risk -- data breach exposure, regulatory violation, and reputational harm -- through a documented chain of custody from decommissioning to final disposition.
For enterprise IT teams, ITAD is not a one-time event. It is a recurring operational process that should be integrated into broader IT asset lifecycle management. The organizations that handle it best treat disposition as a discipline, not a project.
Why ITAD Is More Complicated Than Most Organizations Expect
The volume problem. Shorter hardware refresh cycles mean more devices retiring faster. A four-year laptop refresh on a 10,000-seat enterprise produces 2,500 decommissioned devices per year. Add servers, mobile devices, and networking equipment, and the volume adds up quickly. Ad hoc disposition processes that work for 50 devices fail at that scale. Without a structured program, assets accumulate in storage, move without documentation, or get handed to vendors without proper vetting.
The data liability does not end when the device powers down. Sensitive data persists on decommissioned hardware until it is professionally sanitized or physically destroyed. A decommissioned server returned to a vendor without certified data erasure is a live liability. In 2020, Morgan Stanley was fined $60 million by federal regulators after failing to properly decommission data center equipment containing client data. Morgan Stanley's vendor failed to properly wipe the hardware and sold the devices downstream without adequate data destruction -- a vendor management failure that exposed the bank to full liability. That case is the clearest enterprise-level illustration of what improper ITAD costs.
Most organizations discover their ITAD problem too late. This is the part that rarely gets discussed. The decisions that determine how complex, costly, and risky your ITAD process will be were made years before disposition begins. How assets were acquired, whether they were tracked throughout their lifecycle, what data classification was applied to them, and what contractual obligations were attached -- all of these shape what end-of-life looks like. ITAD is not a disposal problem. It is a procurement and lifecycle planning problem that surfaces at disposal.

What a Compliant ITAD Process Actually Looks Like
Asset inventory and classification. The process begins with knowing exactly what you have. This means linking disposition workflows to your CMDB or ITAM system so every device has a documented lifecycle history. Assets should be classified by data sensitivity, regulatory scope, and business criticality before any disposition decision is made. Shadow assets -- devices that have drifted off the inventory without formal decommissioning -- are one of the most common sources of compliance gaps in enterprise environments.
Data sanitization. NIST SP 800-88 Revision 2, updated in September 2025, is the governing standard for media sanitization in enterprise environments. It defines three levels: Clear, which removes data using standard read/write commands and is appropriate for lower-sensitivity assets; Purge, which applies advanced techniques such as cryptographic erasure or degaussing to make recovery infeasible even with laboratory tools, used for assets leaving organizational control; and Destroy, which involves physical shredding or disintegration and is required for the highest-sensitivity data classifications. The appropriate method depends on the asset type, the data it contained, and your regulatory obligations.
Disposition path decision. Not every retired asset should be destroyed. A value-first hierarchy means evaluating redeployment within the organization first, then remarketing to secondary buyers, then recycling, and only then destruction. Enterprise-grade servers, recent-generation laptops, and networking gear frequently retain meaningful secondary market value that organizations leave on the table by defaulting to shredding.
Chain of custody and documentation. Every asset must be tracked from pickup through transport, processing, and final disposition. A qualified ITAD provider issues serialized asset tracking records, certificates of data destruction, downstream vendor disclosures, and a final disposition report. Without this documentation, your organization cannot demonstrate compliance during an audit, and in regulated industries, that gap carries real consequences.
ITAD Compliance: What the Regulatory Landscape Actually Requires
Most ITAD compliance guides stop at GDPR and HIPAA. That is a reasonable starting point, but it understates the scope of obligations that enterprise IT teams face, particularly those managing assets across multiple geographies.
Data sanitization standards. NIST SP 800-88 Rev 2 (September 2025) is the primary reference for federal agencies and a widely adopted benchmark in regulated industries. It governs the method and verification of sanitization, not just the outcome. Documentation of the sanitization step -- who performed it, what method was used, and on which specific assets -- is required to demonstrate compliance.
U.S. regulatory frameworks. HIPAA imposes specific obligations on covered entities and business associates regarding the destruction of protected health information on hardware. HIPAA violation penalties were updated for 2025, with fines now ranging from $145 per violation to over $2 million per violation depending on level of culpability. California's CPRA includes data deletion obligations that extend to end-of-life hardware in some interpretations. State-level e-waste laws add a further layer, with California's DTSC imposing penalties of up to $70,000 per violation per day for improper disposal.
The Basel Convention -- what most enterprise IT teams are not tracking. As of January 1, 2025, amendments to the Basel Convention brought both hazardous and non-hazardous e-waste under its Prior Informed Consent framework for cross-border shipments. This is a significant change for any enterprise managing ITAD across international operations. Cross-border movement of decommissioned IT equipment -- including laptops, servers, and networking gear classified as e-waste -- now requires advance notification and consent from receiving countries. For enterprises that previously shipped retired assets to regional hubs or partner facilities abroad, this changes the logistics and documentation requirements materially.
WEEE Directive (EU). Enterprises operating in European markets are subject to the Waste Electrical and Electronic Equipment Directive, which mandates separate collection, treatment, and recycling of electronic equipment. Compliance obligations vary by member state in their implementation details.

ITAD Certifications: What to Look for in a Provider
Certifications are the most reliable indicator of a provider's operational standards, but they are not all equivalent, and scope matters as much as the certification itself.
R2v3 (Responsible Recycling). The third version of the R2 standard is the leading certification for environmentally responsible IT disposition. It requires vendors to prioritize reuse and refurbishment, manage hazardous materials responsibly, and document downstream vendor relationships. R2v3 is the current version; verify that a provider holds v3 specifically, not an earlier iteration.
NAID AAA. Issued by the National Association for Information Destruction, NAID AAA certification covers data destruction protocols including secure erasure, physical destruction, and chain-of-custody tracking. It is the primary certification to require for providers handling data-bearing assets.
e-Stewards. e-Stewards certification specifically addresses export controls, prohibiting the shipment of hazardous e-waste to developing countries and holding providers to strict downstream accountability standards.
ISO 14001. An environmental management system certification, relevant for organizations with ESG reporting obligations or sustainability commitments.
One honest caveat: certifications verify that a provider's processes meet a defined standard. They do not guarantee outcomes on every asset. Verify that the certification scope covers your specific asset types and jurisdictions, not just the provider's primary operating location.

ITAD at Global Scale: A Different Challenge Entirely
The majority of ITAD content available to enterprise IT teams assumes a single-country operation. For organizations managing technology across multiple regions, that framing is not just incomplete -- it can create compliance gaps that are difficult to close after the fact.
Global ITAD introduces several layers of complexity that do not exist in domestic programs. First, regulatory recognition of certifications is not uniform. R2 and e-Stewards carry strong credibility in North American markets, but recognition and enforcement standards differ across the EU, Asia-Pacific, and emerging markets. An ITAD provider that is certified for operations in the United States may not have equivalent coverage or downstream controls in every country where an enterprise has retired assets.
Second, the January 2025 Basel Convention amendments create new documentation requirements for any organization moving retired equipment across borders. Enterprises that previously relied on informal logistics arrangements to consolidate assets at regional disposition hubs now need to build Prior Informed Consent documentation into those workflows.
Third, data protection obligations vary by country in ways that affect how sanitization must be performed and documented. The GDPR's right to erasure has specific implications for data on hardware being transferred or disposed of, and interpretations of what constitutes adequate sanitization under GDPR differ from NIST 800-88 in some respects.
Managing ITAD at global scale requires not just a certified provider, but one with genuine operational presence -- owned facilities, vetted partners, and documented chain of custody -- across the jurisdictions where assets are being retired. The alternative is a patchwork of regional arrangements that may individually satisfy local requirements but fail to provide the consolidated audit trail that enterprise compliance programs require.
Value Recovery: What Organizations Are Leaving on the Table
According to Future Market Insights, remarketing and value recovery is the fastest-growing segment in the ITAD market, accounting for nearly 28% of the market by 2025. That growth reflects a shift in how enterprises think about retired hardware. End-of-life does not mean end of value.
Enterprise-grade servers, recent-generation laptops, and networking equipment frequently retain significant secondary market value. A server retired at the end of a four-year refresh cycle may represent three or more years of productive life in a secondary deployment. The organizations that recover this value are those with the asset visibility and market relationships to route equipment appropriately rather than defaulting to destruction.
The most common reason value goes unrecovered is process design. Organizations that lack a condition assessment step in their ITAD workflow default to recycling or destruction because it is the path of least resistance. A value-first approach requires evaluating each asset class against current secondary market conditions before assigning a disposition path.
Value recovery offsets ITAD cost. For CFOs evaluating the total cost of a hardware refresh program, the residual value recovered through remarketing is a real line item, not a rounding error. Managing it properly requires either internal secondary market expertise or an ITAD partner with established remarketing channels.
How Acquisition Decisions Shape ITAD Outcomes
The most underappreciated variable in enterprise ITAD is not vendor selection or sanitization methodology. It is how the assets were acquired in the first place.
Organizations that own their hardware carry the full weight of disposition: compliance documentation, data destruction costs, logistics, residual value management, and the liability exposure that comes with any gap in the process. That burden falls entirely to the IT and procurement team, often without dedicated resources.
Enterprises that lease hardware under a fair market value structure operate differently at end of life. The lessor retains a financial stake in the asset's residual value throughout the lease term, which means the lessor has a structural incentive to manage disposition responsibly. The asset's condition, chain of custody, and end-of-term routing directly affect the lessor's portfolio returns. That alignment of incentives is not incidental to the ITAD outcome -- it is baked into the contract structure.
This is not an argument that leasing eliminates ITAD responsibility. Data security obligations stay with the organization regardless of ownership structure. But it does mean that enterprises evaluating their ITAD program would benefit from reviewing how their acquisition model distributes disposition complexity, and whether that distribution is intentional.

Talk to CHG-MERIDIAN About Your IT Lifecycle Strategy
Managing IT asset disposition well requires visibility into your hardware from day one, not just at end of life. CHG-MERIDIAN works with enterprise IT and procurement teams to build lifecycle structures that reduce disposition complexity, protect against compliance exposure, and recover residual value at end of term.
If you are approaching a hardware refresh or evaluating how your current acquisition model affects your ITAD obligations, we are happy to walk through the options.

Frequently Asked Questions
What is the difference between ITAD and IT asset recycling?
Recycling is one possible outcome within an ITAD process. ITAD encompasses the full governance process: data sanitization, asset tracking, value recovery, regulatory compliance, and certified recycling or destruction -- all under a documented chain of custody. A recycler processes materials. An ITAD program manages risk. Treating the two as equivalent leaves organizations exposed on data security and compliance.
What certifications should an ITAD provider hold?
At minimum, look for NAID AAA for data destruction, R2v3 for environmentally responsible recycling and remarketing, and e-Stewards if cross-border asset movement is involved. ISO 14001 is relevant for organizations with ESG reporting obligations. Verify that the certification scope covers your specific asset types and the jurisdictions where your assets are located -- not just the provider's headquarters location.
How does ITAD relate to data center decommissioning?
Data center decommissioning is one of the most complex ITAD scenarios an enterprise encounters. The assets involved -- servers, storage arrays, networking equipment -- are high value, tightly integrated, and almost always contain sensitive data. Decommissioning typically happens during server refreshes, storage migrations, cloud transitions, or facility closures. ITAD should be part of the decommissioning plan from the start, not a cleanup step at the end. Timing, documentation, and replacement planning all depend on having a clear disposition path in place before the first rack is pulled.
What does chain of custody mean in ITAD?
Chain of custody means every asset is tracked from collection through transport, processing, and final disposition, with documentation at each handoff. A qualified ITAD provider issues serialized asset records, certificates of data destruction, downstream vendor disclosures, and a final disposition report. If your organization cannot show where an asset was, who handled it, and what happened to it at each stage, the chain of custody is broken -- and that gap is what auditors and regulators look for.
How do the 2025 Basel Convention amendments affect enterprise ITAD?
As of January 1, 2025, the Basel Convention's Prior Informed Consent framework now applies to all cross-border e-waste shipments, including both hazardous and non-hazardous electronic waste. For enterprises moving retired IT equipment across borders -- whether to regional hubs, partner facilities, or ITAD vendors in other countries -- this creates new notification and documentation requirements. Any organization with international operations that has not reviewed its cross-border disposition logistics against the amended Basel requirements should do so before its next major hardware refresh.
Can enterprises recover value from retired IT assets?
Yes, and most do not recover as much as they could. Enterprise-grade servers, recent-generation laptops, and networking equipment frequently retain meaningful secondary market value at the end of a standard refresh cycle. Remarketing through a qualified ITAD provider with established secondary market channels is the most reliable path to recovering that value. The key requirement is a condition assessment step in the ITAD workflow -- without one, organizations default to recycling or destruction and leave recoverable value behind.
Get in Touch
Simon Harrsen leads CHG-MERIDIAN's North American operations, helping organizations optimize technology investments through smarter lifecycle management. Connect with him to discuss how your business can reduce costs and increase flexibility.

Stay Connected
Learn more
 IT Lifecycle Management
ITAD starts at procurement, not disposal. Learn how to manage hardware across its full lifecycle.
IT Lifecycle Management
ITAD starts at procurement, not disposal. Learn how to manage hardware across its full lifecycle.
 FMV Lease vs. $1 Buyout Lease: How to Choose the Right Structure for IT Equipment
Your lease structure shapes your ITAD complexity. Learn what each option means at end of life.
FMV Lease vs. $1 Buyout Lease: How to Choose the Right Structure for IT Equipment
Your lease structure shapes your ITAD complexity. Learn what each option means at end of life.
 IT Infrastructure Modernization
Modernization triggers ITAD. Learn how to plan upgrades with end-of-life built in from the start.
IT Infrastructure Modernization
Modernization triggers ITAD. Learn how to plan upgrades with end-of-life built in from the start.